In the digital age, fiber optic cables form the backbone of global communication. Yet, beneath their speed and efficiency lies a vulnerability that could threaten our privacy. What if the very lines we trust to transmit information could also be used to spy on us? The implications are profound.
Chapter 01
The Silent Eavesdropper
Fiber optics are faster and more reliable than traditional copper cables, yet they harbor hidden risks.
Understanding Fiber Optic Vulnerabilities
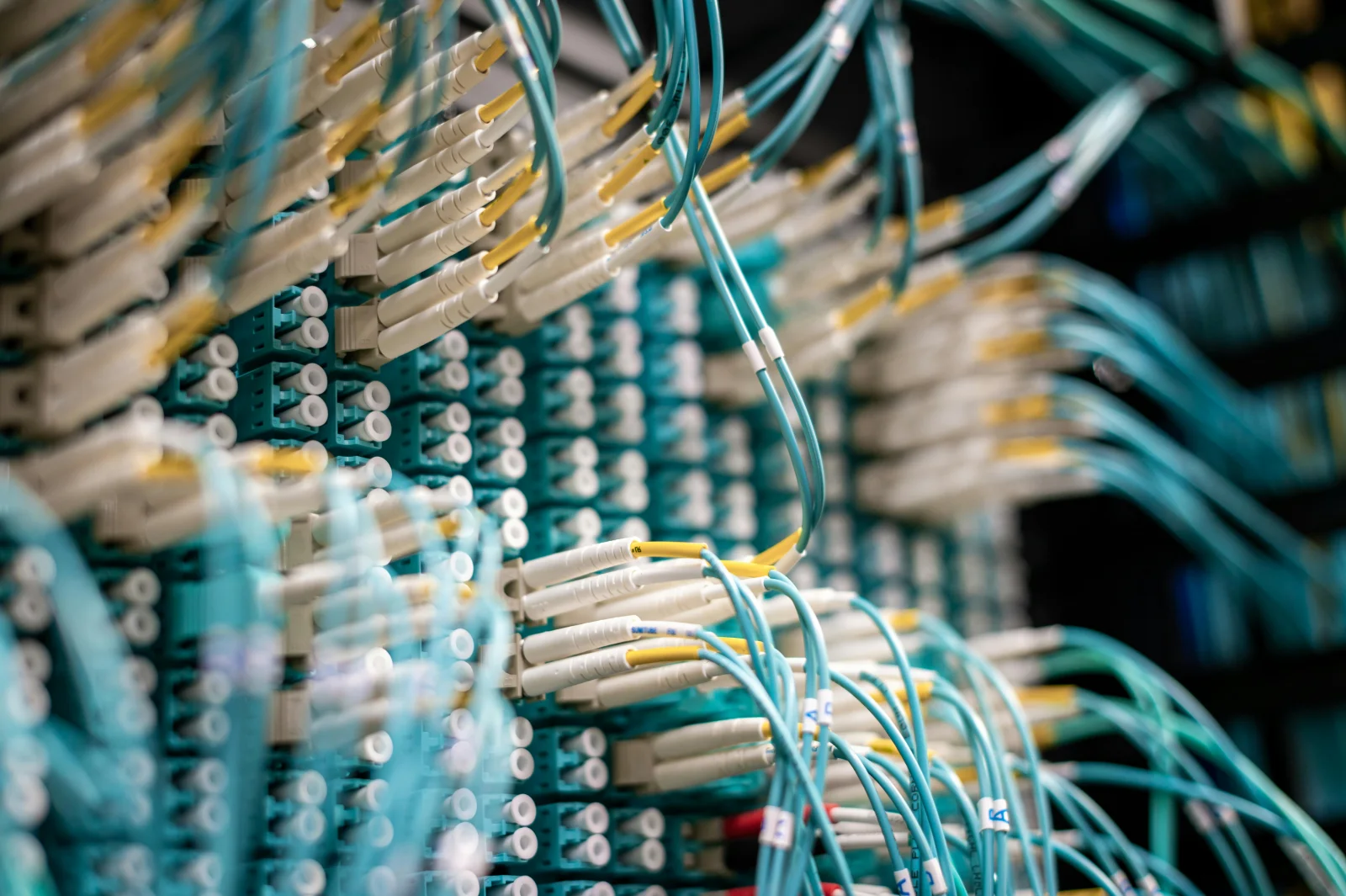
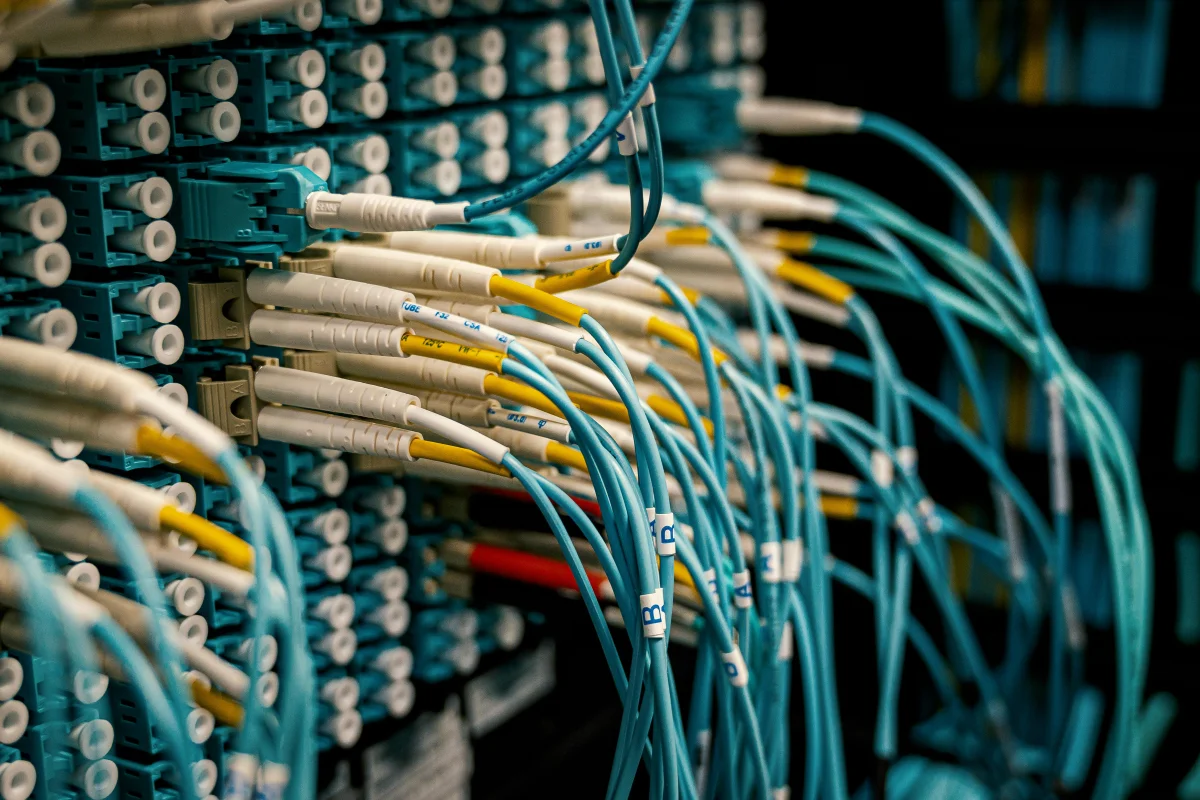
Fiber optic cables have revolutionized how we send and receive data. With their ability to transmit information using light, they offer unparalleled speed and bandwidth. However, this technology is not without its security flaws.
- Physical Tapping: Unlike wireless networks, fiber optics can be physically tapped without significant data loss.
- Signal Interference: Techniques like bending can introduce minimal signal interference, making detection challenging.
- Infrastructure Complexity: The expansive and intricate nature of fiber networks can make security oversight difficult.
The Mechanics of Tapping
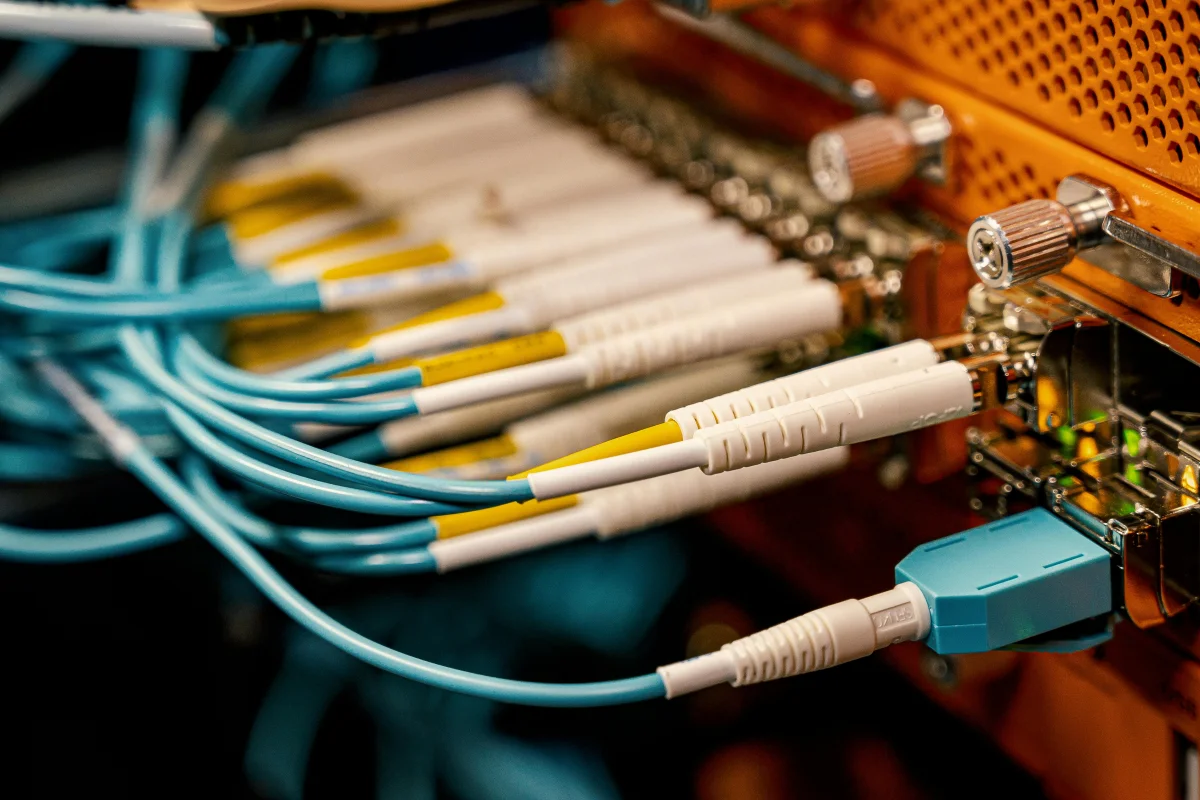
Fiber tapping involves bending the cable slightly to allow light to escape. This light can then be captured and analyzed. While this might seem like a scene from a spy movie, it’s a real and growing threat.
Historical Context
The history of espionage is filled with tales of wiretapping. Fiber optics may seem modern, but they are not immune to age-old tactics. The difference? The tools have evolved, becoming more sophisticated and harder to detect.

The real risk lies not in the technology itself but in how it's protected.
Bruce Schneier
Chapter 02
Securing the Light
As fiber optic networks expand, so do the challenges to secure them.
Narrative flow
Scroll through the argument
01
Detection Mechanisms
Implementing advanced monitoring systems to detect unusual activities along the cables.
02
Encryption Enhancement
Enhancing encryption methods to ensure captured data remains unreadable.
03
Infrastructure Resilience
Building robust infrastructure that can withstand physical and cyber threats.
Emphasizing Encryption
Encryption remains the cornerstone of data security. Even if data is intercepted, strong encryption ensures it remains unreadable. This is crucial in fiber optics where the potential for undetected tapping is high.
Infrastructure Challenges
Building secure fiber optic networks is not just about technology—it’s about strategy. Network operators must consider not only current threats but also anticipate future vulnerabilities.
Misconceptions
There’s a common belief that fiber optics are inherently secure due to their design. While it’s true that they offer certain advantages, security must be actively maintained and updated.
Fiber Optic Security Insights

The digital world is evolving at breakneck speed, and with it, the methods to secure our data. Fiber optics, while a marvel of modern engineering, require vigilance and innovation to ensure they remain secure. As we continue to build our networks, the challenge will be to do so with security at the forefront.
In conclusion, fiber optic networks represent a double-edged sword. They offer unmatched speed and capacity but also present unique security challenges. Staying ahead requires innovation, vigilance, and a commitment to robust security practices.